#Vault7: How the CIA steals hacking fingerprints to cover its tracks

The CIA can hide its own fingerprints from its hacking exploits and attribute blame to others, such as Russia and China, according to WikiLeaks’ Year Zero confidential data
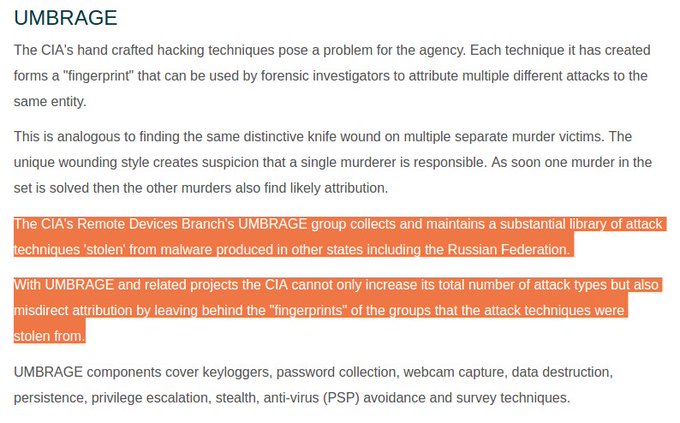
Every hacking technique leaves a “fingerprint” which, when collated, can be used to connect different attacks and tie them to the same culprit.
The CIA’s Remote Development Branch (RDB)’s Umbrage sub-group collects an archive of hacking exploits created by other actors, like Russia and other hackers, and leaves this false trace for others to detect.
Umbrage captures and collects keyloggers, passwords, webcam captures, data destruction, persistence, privilege escalation, stealth, anti-virus (PSP) avoidance and survey techniques.
This allows the CIA to not only steal other’s hack techniques, but falsely apportion blame to those actors.
Hacking Team
An Umbrage document shows how the agency mined information from a breach of Italian “offensive security” vendor Hacking Team, that boasts governmental and law enforcement clients.
Some 400GB of data including “browser credential stealing” and “six different zero-day exploits” was released in the breach, which Umbrage studied and added to its repository.
DNC hack
#Vault7 This is how the CIA uses false 'fingerprints' to frame others, such as Russia (ie DNC hack) #Vault7 #wikileaks@TuckerCarlson
Who needs enemies like Russia when you have got friends like the CIA and the Deep State. Read #Vault7truthfeed.com/breaking-wikil…
In the case of the Democratic National Committee (DNC) hack, which reports have connected to Russia, the fingerprints used to link blame to Russian hackers may have been manipulated.
Crowdstrike, a private security firm linked to the Atlantic Council, found the hackers who accessed the DNC emails (and those of Clinton campaign chair John Podesta) left “clues,” which Crowdstrike attributed to Russian hackers.
Malware dug into the DNC computers was found to be programmed to communicate with IP addresses associated with Fancy Bear and Cozy Bear - hacking groups that Crowdstrike says are controlled by Russian intelligence.
Metadata found in a file contained modifications by a user using Cyrillic text and a codename Felix Edmundovich.
#Vault7 - there goes the whole CIA narrative about Russian hacking of the 2016 election. wikileaks.org/ciav7p1/
While the documents released don’t tie Crowdstrike to the CIA’s Umbrage program, the data demonstrates how easily fingerprints can be manipulated, and how the CIA’s vast collection of existing malware can be employed to disguise its own actions.






0 Comments:
Post a Comment
Subscribe to Post Comments [Atom]
<< Home